RiskIntelligence Patient Privacy Monitor
Ensure continuous compliance with privacy laws while reducing 90% of the cost
Purposely built for healthcare organizations to monitor and analyze Healthcare system logs to detect privacy breaches with advanced Artificial Intelligence and Machine Learning technology
Our Amazing Clients
automated privacy log review process with 90% cost reduction



Comply with healthcare privacy legislations
RiskIntelligence privacy monitor (RPM) automatically monitors and analyzes the healthcare system data with advanced AI/ML and UEBA algorithms to ensure compliance with healthcare privacy legislation and regulations.
PHIPA s.10.1(1)
Electronic audit log
10.1 (1) Subject to any prescribed exceptions, a health information custodian that uses electronic means to collect, use, disclose, modify, retain or dispose of personal health information shall,
(a) maintain, or require the maintenance of, an electronic audit log described in subsection (4);
(b) audit and monitor the electronic audit log as often as is required by the regulations; and
(c) comply with any requirements that may be prescribed. 2020, c. 5, Sched. 6, s. 3.
164.312 Technical safeguards.
164.312 (b) Standard: Audit controls. Implement hardware, software, and/or procedural mechanisms that record and examine activity in information systems that contain or use electronic protected health information.
164.308 Administrative safeguards.
164.308 (a)(1)(ii)(D) Information system activity review (Required). Implement procedures to regularly review records of information system activity, such as audit logs, access reports, and security incident tracking reports.
Transform Privacy Compliance from Reactive to Real-Time
Replace tedious manual log reviews with an advanced, AI-driven analysis solution purpose-built for healthcare privacy monitoring. Stop searching for breaches after the damage is done.
Continuous AI Detection
Manual audits in Excel take weeks and miss the subtle signs of insider threats. Our User Entity Behavior Analysis (UEBA) works 24/7, continuously analyzing millions of EHR log events to catch curiosity snooping and data extraction the moment they happen.
Investigation-Ready Context
Don’t drown in false positives. RiskIntelligence cross-references access logs with clinical schedules and care team assignments automatically. When an alert triggers, you get an investigation-ready evidence package, cutting resolution time from days to minutes.
Defensible Compliance
Prove your due diligence to regulators. Ensure strict compliance with HIPAA and PHIPA with a solution that guarantees secure Canadian data residency, automated reporting, and a dramatic reduction in breach detection costs.
How It Works
1. Collecting Logs
RPM can automatically collect logs from healthcare systems. Or the logs can be uploaded to RPM.
2. Modeling Behavior
RPM learns each clinician’s normal behavior and builds behavior profiles.
3. Detecting Anomalous
RPM assesses the user’s activity based on the normal behavior profile to detect anomalous activities.
4. Investigating Alerts
RPM provides explainable alerts and advanced tools for alert investigation.
Key Features
Be empowered to effectively detect, investigate, and manage privacy breaches!
Detection
Utilize Machine Learning and User Entity Behavior Analysis (UEBA) to thoroughly analyze electronic audit logs and precisely uncover any privacy breaches.
Alert
Deliver real-time alert notifications for privacy breaches, along with detailed reports on privacy breach indicators, alerts, and access.
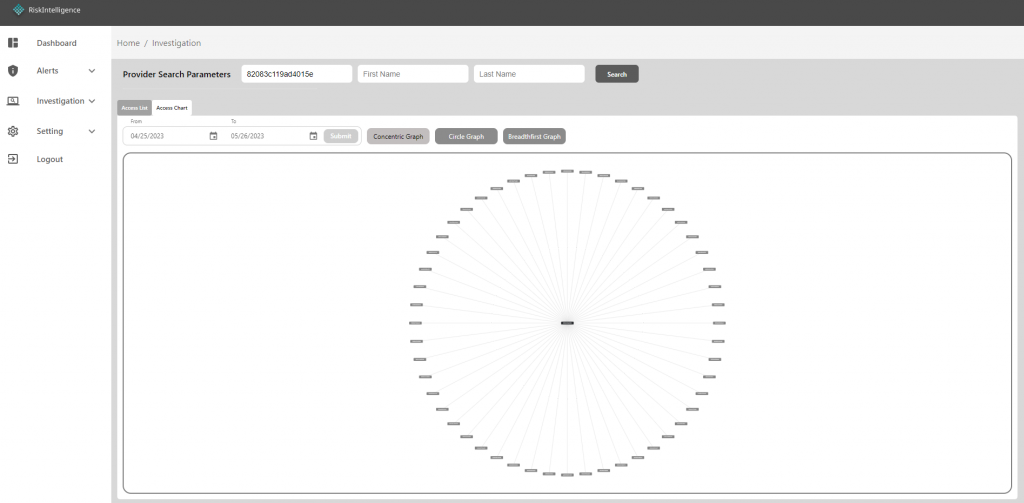
Investigation
Conduct thorough examinations of potential privacy violations by analyzing explainable risk indicators and anomalous activities.
Manual Audit
Correlate, sort, filter, visualize audit logs to manually inspect clinicians' access to patients to identify privacy breaches.
Analysis Tuning
Optimize analysis engine to enhancing accuracy and reducing false-positives.
Management
Manage privacy breaches by viewing, validating, and resolving detected privacy risk indicators and alerts.
Why Choose RiskIntelligence to automate privacy log review?
At RiskIntelligence, we understand how important it is for healthcare service providers to protect their patients’ personal health information and comply with privacy law, legislation, and regulation. That’s why we have developed a state-of-the-art Privacy Monitor cloud service that utilizes Machine Learning and Artificial Intelligence technology. Our solution monitors and analyzes healthcare system logs to detect privacy risks and provides real-time alerts so that healthcare providers can take proactive measures to safeguard their patients’ sensitive information. With our solution, you can have peace of mind knowing that your patients’ privacy is being diligently monitored. Contact us today to learn more about our Privacy Monitor Solution.
Our RiskIntelligence Privacy Monitor solution reduces 90% of manual log review costs. Our solution is more than 50% less than the cost of the competitor solutions.
Our platform leverages cutting-edge analytical techniques, including User and Entity Behavior Analysis (UEBA), Machine Learning (ML), and Artificial Intelligence (AI), to effectively detect privacy and security risks.
Our solution continuously learns and models the user’s behavior to support evolving clinical processes, resulting in a significant reduction in false positives and false negatives.
Our solution tracks the clinician’s activities over several years, allowing the privacy officer to review and analyze the clinician’s access to patients to detect anomalous activities.
Our specialists have excellent knowledge and experience in privacy breach detection and investigation to assist you in fine-tuning the detection algorithms to reduce false positives.
FAQ
How does the solution detect privacy breaches?
Our Privacy Monitor solution leverages machine learning (ML) and artificial intelligence (AI) to create individual user behavior models. This enables the detection of anomalous activities based on each user’s unique behavioral patterns.
How acurate is the privacy breach detection?
While our Privacy Monitor solution excels at identifying anomalies within audit logs, not all anomalies necessarily represent privacy breaches. Generally, the system allows for parameter adjustments to optimize detection accuracy and minimize false positives.
What should I do with the alerts?
Our Privacy Monitor solution provides easy-to-use features to investigate the alerts. You can view all relevant data to investigate and confirm potential breaches.
How do you protect our data that contains PHI?
At RiskIntelligence, we prioritize the security of your sensitive protected health information (PHI). We implement robust security safeguards including data encryption at rest, role-based access control (RBAC), comprehensive user activity auditing, and web application firewall (WAF) inspection of all traffic. Additionally, we are actively pursuing ISO 27001 certification and a SOC 2 report to demonstrate our commitment to the highest security standards.
What data is required to detect privacy breach?
RiskIntelligence Privacy Monitor solution analyzes access logs detailing provider access to patient/client data to detect potential privacy breaches. It is not required, but with additional provider and patient/client data (from HR system and patient registration system), the log data can be further enriched to increase detection accuracy.
How to start using the privacy monitoring solution?
You can simply export the audit log from your healthcare system and upload it to the RiskIntelligence Privacy Monitor to start detecting privacy breaches. The RiskIntelligence Privacy Monitor can also automatically retrieve the audit log from your healthcare system through API or a log collection agent.
How do I know if the privacy monitoring solution works effectively on our logs?
Experience the power of our Privacy Monitor solution firsthand with a complimentary trial. Simply upload your healthcare system’s audit logs to our secure web portal, and you’ll be able to access insightful results and experience our user-friendly interface. To get started, contact us today.
Can the solution be used for manual audit?
Our Privacy Monitor solution empowers manual privacy audit with comprehensive investigation functions. Users can efficiently search and view detailed access events associated with any provider or client/patient with visualization.